Given a scenario, utilize threat intelligence to support organizational security
Attack frameworks
- MITRE ATT&CK - MITRE ATT&CK® is a globally-accessible knowledge base of adversary tactics and techniques based on real-world observations. The ATT&CK knowledge base is used as a foundation for the development of specific threat models and methodologies in the private sector, in government, and in the cybersecurity product and service community. (Taken from the MITRE website)
- The Diamond Model of Intrusion Analysis - looks at the relationships and characteristics of four components: the adversary, capabilities, infrastructure, and victims. To see more Click Here PDF Warning.
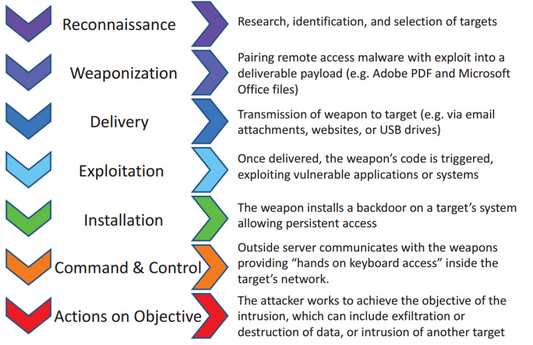
- Kill chain - Developed by Lockheed Martin, the kill chain is an intrusion identification and prevention model.
Threat Research
- Reputational - intelligence data that has been analysed from past activities. If attacks are generated from a certain IP address, it's reputational score will decrease.
- Behavioral - examines the network behaviors for anomalies using NetFlow, protocol, and packet analysis to establish baselines and alert on outliers.
- Indicator of compromise (IoC) - any activity, artifact, or log that is associated with an attack pattern. These can include virus signatures, known malicious file hashes, domain names, IP addresses.
- Common vulnerability scoring system (CVSS) - a system that ranks vulnerabilities by severity on a scale of 0 to 10:
- 0: no issues
- 0.1 - 3.9: Low
- 4.0 - 6.9: Medium
- 7.0 - 8.9: High
- 9.0 - 10.0: Critical
- Base - Characteristics of a vulnerability that are constant over time and user environments
- Temporal - Characteristics of a vulnerability that change over time but not among user environments.
- Environmental - Characteristics of a vulnerability that are relevant and unique to a particular user's environment
- Attack Vector (AV) - how the attacker could exploit the vulnerability:
- L - Local, means the attacker would need physical or logical access to the system.
- A - Adjacent, means the attacker would need to be on the local network.
- N - Network, the attacker needs to have any network access.
- P - Physical, the attacker needs physical access to the system.
- Attack Complexity (AC) - the difficulty of exploiting the vulnerability:
- H - High, the vulnerability requires special conditions that may be hard to find.
- L - Low, the vulnerability does not require any special conditions.
- Privileges Required (PR) - The authentication an attacker would need to exploit the vulnerability
- H - High, the attacker would need high level of access (administrative)
- L - Low, the attacker would need basic level of access
- N - None, the attacker would need no level of authentication.
- User Interaction (UI) - the requirement for interaction with the human user of the system
- N - None, requires no user interaction.
- R - Required, the vulnerability requires some action by the user
- Scope (S) - If a vulnerability in on component impacts components beyond its security scope
- U - Unchanged, the vulnerability only affects resources managed by the same security authority.
- C - Changed, the vulnerability can affect resources beyond the security scope managed by the security authority of the component.
- Availability (A) - If a vulnerability disrupts the service or system
- N - None, there is not availability impact.
- L - Low, system performance is degraded.
- H - High, all access to the system is down.
- Confidentiality (C) - Information disclosure that may occur if the vulnerability is exploited.
- N - None, no confidentiality impact.
- L - Low, some access to information may occur.
- H - High, all information on the system could be compromised.
- Integrity (I) - Data alteration might occur.
- N - None, there is no data integrity impact.
- L - Low, there may be some data alteration.
- H - High, all information may be altered.
Threat modeling methodologies
- Adversary capability - Different types of attackers have different types of capabilities. Capabilities can be skill level, resources, limits, visibility, objective, and outcome.
- Total attack surface - all the points where vulnerabilities exist. These can be vulnerabilities the organization knows, or doesn't know about. It is important to develope a formalized process to look for and test vulnerabilities.
- Attack vector - the path or means that an attack is carried out including: phishing, malware, code injection, social engineering, exploiting unpatched vulnerabilities.
- Impact - if an asset is compromised, how much of an impact will that have on the organization.
- Likelihood - what are the chances that a certain vulnerability on a certain asset will be compromised.
Threat intelligence sharing with supported functions
- Incident response - with threat intelligence, it is important for the incident repose team members to keep up to date with the latest trends in threats and how those threats are executed.
- Vulnerability management - vulnerability information needs to be shared with everyone involved in vulnerability management.
- Risk management - a formal process that assess vulnerabilities by the likelihood and impact of a compromise, sharing this data is critical with all those involved to reduce risk.
- Security engineering - architecting security into the design of a system or set of systems, it is imperative that threat information is shared with engineers so they can design and build systems securely
- Detection and monitoring - team members that detect and monitor threats within an organization rely on timely sharing of information to identify new threats.
Threat research is keeping up with current threat trends and staying informed so that you can make informed decisions.
Part of the risk management process is evaluating the risk that is present in the organization. A threat modeling methodology create a framework for evaluating this risk. These are factors to consider in a threat modeling methodology:
It is important to share intelligence information with other organizations and other departments within your own organization that may be impacted.
